2022 was a big year for us.
In this recap (not ReCap… read on to learn about ReCaps), we’ll share a non-exhaustive list of some of our accomplishments from the past year, starting with our company updates, then highlighting key development work across our open-source products and libraries.
As the builders of open-source software (essentially public goods), we have to toot our own horn a little bit.
Our Company
💡Fundraising
In April, we announced a $34M Series A round led by a16z crypto. This funding enables us to lead research efforts in cutting-edge privacy and usability technology for identity, while growing our product teams and executing partnerships across the Web3 ecosystem. You can learn more in our announcement here.

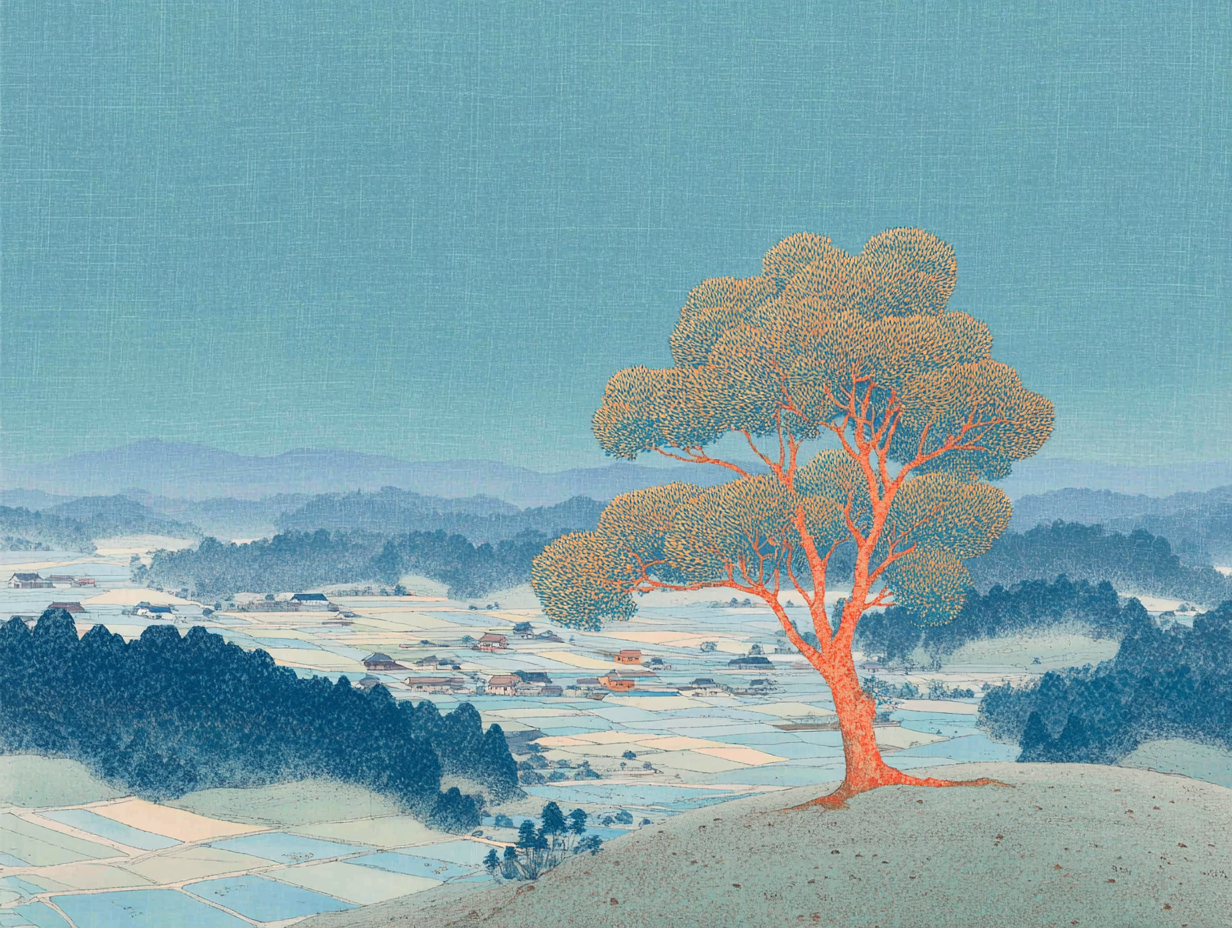
🌲Our Team
Our Spruce team grew in 2022, but we’re still small and mighty! Spruce is currently across three continents and eight countries.
Our team is globally distributed and remote-first. Rather than having a physical office, we gather in different locations twice per year for multi-day workshops and team events.
🎉Events and Hackathons
- We sponsored bounties at ETHDenver, ETHAmsterdam, and Graph Hack, working with developers to apply Sign-In with Ethereum to core workflows in hackathon projects.
- We also sponsored the event dinners and were the Diversity & Inclusion sponsor for the Internet Identity Workshop in Mountain View, California.
- We attended and spoke at various conferences around the world, including Devcon, Oktane, and more.
🌍Standards and Working Groups
Spruce participates in various working groups and has implemented and architected various global emerging identity standards, such as W3C Verifiable Credentials, Sign-In with Ethereum, and more. Here are some highlights from our participation this year:
- We co-authored, built, and supported Sign-In with Ethereum (EIP-4361), which moved from “Draft” to “Review” in July on the Standards Track.
- We authored and built additional specifications that extend Sign-In with Ethereum, with one being ReCaps (EIP-5573), enabling SIWE to include human-readable authorizations.
- We participated in the Jobs for the Future (JFF) Plugfest to demonstrate the interworking of Verifiable Credentials with Decentralized Identifiers for learning and employment records (LERs) to be used for proving career qualifications.
- We participated in the ISO/IEC 18013-5 mDL Interoperability Party in Brisbane to demonstrate interoperability with solutions from Microsoft, Ping, and Panasonic for online presentation of driver’s license data to websites in a secure and privacy-preserving manner.
- We spoke about extending Sign-In with Ethereum at the Chain Agnostic Standards Alliance (CASA) Gathering in April.
- Spruce and TBD demonstrated support for all defined JWS algorithms for Data Integrity and JWT proofs for W3C Verifiable Credentials (VCs) and W3C Verifiable Presentations (VPs), which is a significant step towards vendor interoperability.
- We participated in ISO/IEC JTC 1/SC 17 Cards and security devices for personal identification in WG4 and WG10 as delegated experts from different national ISO bodies to work on the mobile driver's license (mDL) and, more generally, the mdoc (mobile ID) standards.
- We participated as co-editor in the W3C Verifiable Credentials Working Group to work on the next version of the Verifiable Credentials Data Model (VCDM) standard.
- We participated in the DIF JWT interoperability presentation profile initiative and demonstrated interoperability with MSFT, Avast, Workday, and IBM at the IIW demo table.
- We participated in the OpenID Foundation AB/C WG as co-editor of the OpenID for Verifiable Presentations (OpenID4VP) and contributors to the OpenID for Credential Issuance (OpenID4CI) to help advance the specifications.
As a company, our most important achievements this year were in the products and libraries we built and maintained, bringing us closer to a future where users control their identity and data across their digital interactions.
Our Open-Source Products
🏠SSX (Self-Sovereign Anything):
We launched SSX in November based on feedback from the community about their experiences installing Sign-In with Ethereum and additional capabilities they wanted. SSX will be the gateway to decentralized identity, combining our core libraries to power user control across the web.

- We made SSX the easiest way to install Sign-In with Ethereum and reduced the amount of code it takes by up to 80%.
- We pioneered DAO login via a collaboration with the Safe team.
- We added support for various frameworks to ensure as easy of a developer experience as possible.
🚗Credible:
With Credible, we are creating a solution to provision mobile driver’s licenses to a smartphone application using ISO/IEC 18013-5, along with the W3C standards for Verifiable Credentials and Decentralized Identifiers, and OpenID for Verifiable Credentials to create secure, privacy-enhancing, and tamper evident identity solutions. We have exciting work underway that we will be able to share soon.

Our Open-Source Libraries
🧱Sign-In with Ethereum:
Sign-In with Ethereum is a new form of authentication that enables users to control their digital identity with their Ethereum account and ENS profile instead of relying on a traditional intermediary.
- Built the Sign-In with Ethereum developer portal with a quick start guide and installation instructions.
- Released libraries for multiple languages, including TypeScript, Rust, Python, Go, and more, ensuring any developer can easily get started.
- Released a Discourse plugin, which enables any self-hosted Discourse forum to enable Sign-In with Ethereum.
- Launched a SIWE integration in the Auth0 (powered by Okta) marketplace, leveraging our OIDC Identity Provider Server.
- Launched the first community-hosted OpenID Connect Identity Provider Server in collaboration with the ENS DAO.
- Specified ReCaps as an extension to SIWE as EIP-5573.
- SIWE received shout-outs from Vitalik, Bankless, and other thought leaders as a top trend to watch in 2023.
- SIWE is currently used by or in the process of being incorporated by hundreds of projects and individual developers - with examples including Tally, Lens Protocol, Unlock, Boardroom, wagmi, WalletConnect, and many more.
🧱DIDKit and ssi:
DIDKit is a cross-platform toolkit for working with W3C Verifiable Credentials, W3C Decentralized Identifiers, and a variety of related data models and protocols.
DIDKit is in production use, powering credential workflows such as those found on Gitcoin Passport. We plan on continuing to enhance and refine DIDKit this year to make it even easier for a developer to get started using W3C Verifiable Credentials.
- We restructured our ssi library into constituent workspace crates to make it easier for developers to import and use.
- We enabled the external signing of verifiable presentations in DIDKit-WASM and VP holder bindings.
- We implemented CacaoDelegationHolderBinding2022 with Sign-In with Ethereum, CACAOs, and ReCaps.
- Added a basic UCAN implementation, a CACAO-ZCAP integration, and contexts for the JFF VC-EDU plugfest.
- We added and improved support for multiple did methods included in DIDKit.
🧱TreeLDR:
We released TreeLDR: a developer tool plus DSL that makes managing data schemas as easy as defining data structures in your favorite statically-typed language.

🧱Rebase:
Rebase is a decentralized service that allows people and organizations to map their identities to cryptographic keys using social media in a user-centric and publicly auditable way.
- We deployed the first reference implementation of a Rebase frontend that allows users to go through workflows to receive Verifiable Credentials.
- We’ve added support for workflows to verify Twitter accounts, GitHub accounts, DNS ownership, Ethereum account ownership, Solana account ownership, Reddit accounts, SoundCloud accounts, and email addresses.
🧱Kepler:
Kepler is a decentralized storage network organized around data overlays called Orbits. Kepler allows users to securely share their digital credentials, private files, and sensitive media to blockchain accounts, all using your Web3 wallet.
- We demonstrated how a user can Sign-In with Ethereum to authenticate with Kepler, use session keys, and store files privately.
- We implemented a capability subsystem, which provides a registry of delegations, invocations, and revocations.
- Rewrote the core SDK functionality in Rust and added a WASM-based SDK, wrapping around the new Rust SDK.
Kepler is currently undergoing active development, and we plan on releasing more information soon on how you can get started using it!
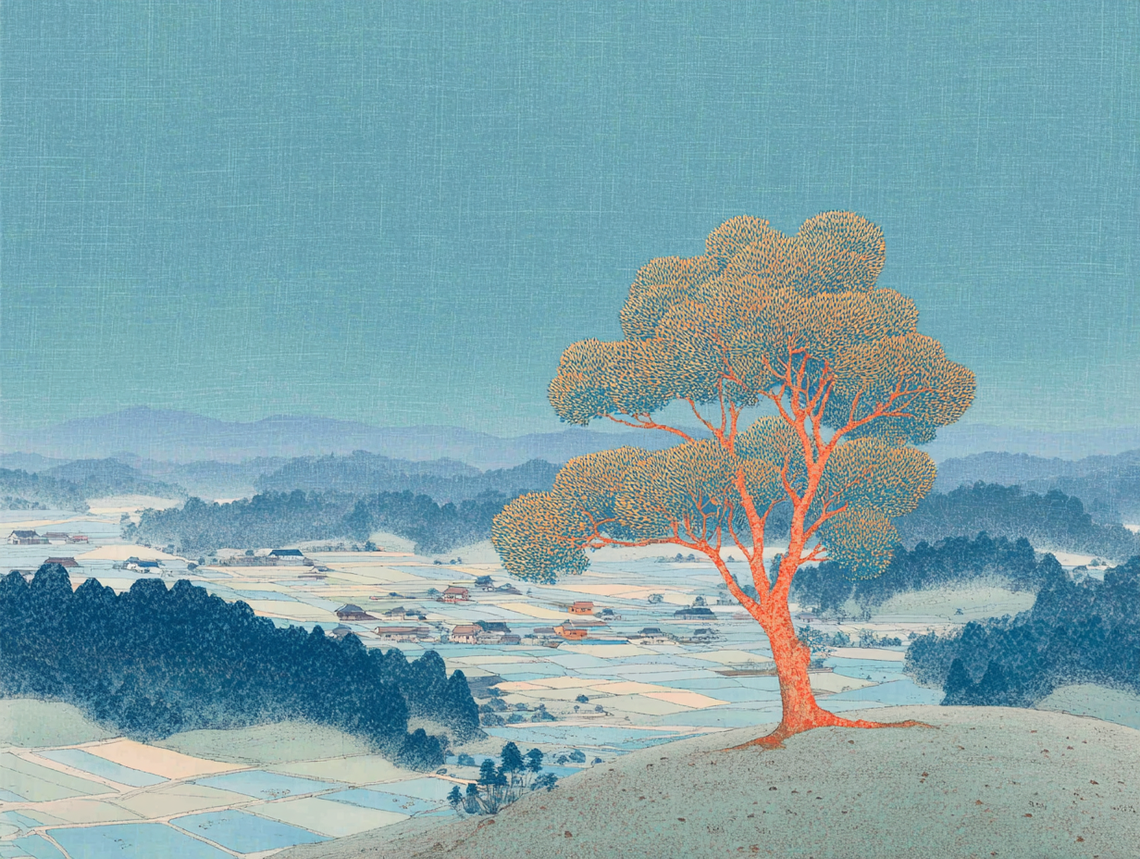
2022 was a banner year for Spruce, but 2023 is shaping up to be even bigger. We share developer updates monthly here that cover all the upgrades, features, and updates to our open-source products and libraries.
About Spruce: Spruce is building a future where users control their identity and data across all digital interactions. If you're curious about integrating Spruce's technology into your project, come chat with us in our Discord.